Blog
Blog
Industry Efforts to Censor Pro-Terrorism Online Content Pose Risks to Free Speech
October 11, 2017By Sophia Cope, Jillian C. York, and Jeremy Gillula In recent months, social media platforms—under pressure from a number of governments—have adopted new policies and practices to remove content that promotes terrorism. As the Guardian reported, these policies are typically carried out by low-paid contractors (or, in the case of YouTube, volunteers) and with little to ...
Blog
Wilayat Internet: Islamic State’s Resilience Across the Internet and Social Media
October 4, 2017By Laurence Bindner, Raphael Gluck This article was originally published in French on Ultima Ratio. Since partly going underground in the deep-web, ISIS exerts continuous pressure to make its propaganda surface on the public web. Adapting constantly to ever more active censorship, ISIS uses the various web platforms in an opportunistic and agile way. Therefore, ...
Blog
Some Reflections on Locating Online Viewers of Jihadist Content in Policy Exchange’s ‘The New Netwar’
September 27, 2017By Lorand Bodo The UK think-tank Policy Exchange recently published a new report on the struggle against online jihadist extremism, or what its authors call “the New Netwar”. The report argues that we are currently struggling to find appropriate ways to combat online jihadist extremism and therefore losing the war online against the so-called ‘Islamic State’ (ISIS). ...
Blog
We Must Separate the Debates on Extremism and Encryption
September 20, 2017By Tom Morrison-Bell The encryption debate has reared its head again as the Home Secretary visited the US to meet with tech firms to understand the work being done to tackle extremism. In an article in The Telegraph, the Home Secretary appears to restate the Government’s desire for some sort of back-door to end-to-end encryption ...
Blog
Islamic State’s Twitter network is decimated, but other extremists face much less disruption
September 13, 2017By Maura Conway and Suraj Lakhani This post is based on findings contained in the VOX-Pol report Disrupting Daesh: Measuring Takedown of Online Terrorist Material and its Impacts published on 15 August 2017. Alongside the fierce battles that have been raging of late in key strongholds of so-called Islamic State (IS) in Syria and Iraq, intense battles against ...
Blog
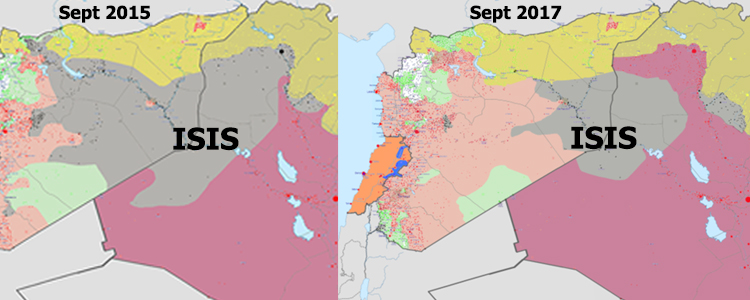
ISIS: From Connective Action to Transnational Insurgency?
September 6, 2017Since late 2016, researchers came to acknowledge both ISIS’ territorial decline and much reduced visibility on mainstream social media networks. They note that its online community of supporters have migrated to encrypted communication channels and that its territory in the Levant has shrunk considerably, which—according to a recent ICSR estimate—impacted on the organisation’s financial resources. ...
Blog
Macedonia’s Jailed Jihadists Try to Recruit Online
July 26, 2017By Haris Fazliu While researching Bringing Down the Digital Caliphate – Breaking the ISIS Brand (under review), for the International Center for The Study of Violent Extremism, ICSVE, I discovered that convicted terrorists in Macedonia linked to ISIS continue to share propaganda online. Jihadists currently serving sentences in Macedonian prisons freely use smartphones to watch videos, ...
Blog
Children are Being Used as Easy Weapons of Propaganda by Terrorist Organisations
July 19, 2017By Amy-Louise Watkin and Sean Looney To involve children in terrorism is an unthinkable prospect. And yet they have become not only targets of violence, but are being used to promote radicalised causes too. This is not just about European or American children being victims of attacks by the so-called Islamic State (IS). Young people who are ...
Blog
Reflections: Terrorism and Social Media Conference 2017
July 12, 2017By Samantha North On 27 and 28 June, in a sleepy Welsh city by the sea, a group of social media and terrorism researchers came together to discuss the latest challenges in the field. I learned a lot, met people doing admirable work and came away inspired with ideas to shape my own research in the ...
Blog
Responding to Terrorists’ Use of Social Media: Legislation, Investigation and Prosecution
July 5, 2017This week’s Blog post is the full text of Max Hill QC’s, the UK’s Independent Reviewer of Terrorism Legislation, keynote speech from last week’s TASM conference at Swansea University. The speech was widely reported on in media, including in The Guardian and The Times. Ed. By Max Hill There can be no doubt that social media plays ...