This article summarises a recent study published in Terrorism and Political Violence.
By Ryan Scrivens, Thomas W. Wojciechowski, Joshua D. Freilich, Steven M. Chermak, and Richard Frank
Despite the ongoing need for researchers, practitioners, and policymakers to identify and assess the online activities of violent extremists prior to their engagement in violence offline, little is empirically known about their online behaviors generally or differences in their posting behaviors compared to non-violent extremists who share similar ideological beliefs particularly. In response, we drew from a unique sample of violent and non-violent right-wing extremists (RWEs) to compare their posting behaviors within a sub-forum of the largest white supremacy forum, Stormfront.
To identify users in the data who were violent RWEs offline and those who were non-violent RWEs offline, a former violent extremist who was actively involved in the North American RWE movement for more than 10 years voluntarily reviewed a list of users who posted in the sub-forum and then selected those who matched one of the two user types. This identification process was done under the supervision of the lead researcher of this project, wherein each time the former identified a user of interest, they were asked to explain in as much detail possible why the user was identified as a violent or non-violent RWE. This was done to verify the authenticity of each user identified by the former. A total of 49 violent and 50 non-violent RWEs were identified from a list of approximately 7,000 usernames. The online content for each user was then identified in the sub-forum data: 12,617 posts from the violent users and 17,659 posts from the non-violent users.
Analyses for the current study proceeded in three phases. First, we plotted the average posting trajectory for all users in the sample, followed by an assessment of the rates at which they stayed active or went dormant in the sub-forum using survival analysis. We then used logistic regression to examine whether specific posting behaviors were characteristic of users’ violence status. Several conclusions can be drawn from this study.
Interestingly, there was a general decline in posting behavior over time for the RWEs in the study. There was also a steady dropout in posting frequency for approximately half of the sample throughout the entirety of the study period. This is a noteworthy set of findings because it suggests that RWEs in the current study – whether violent or non-violent offline – generally do not increase in their posting behavior over time, as is illustrated in Figures 1 and 2.
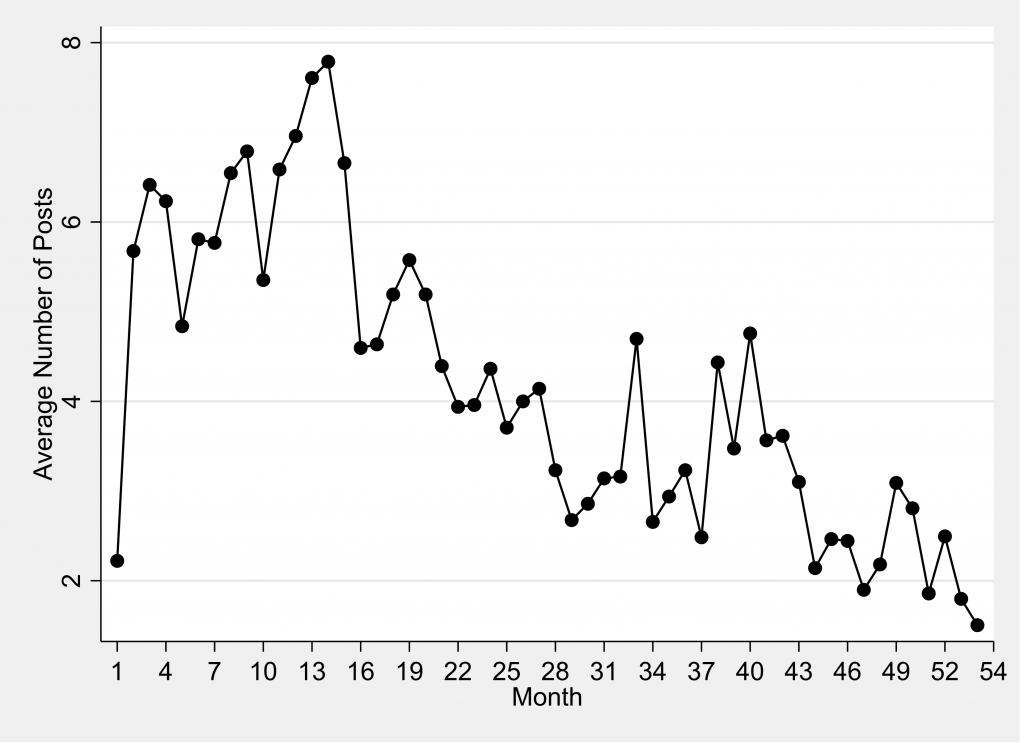
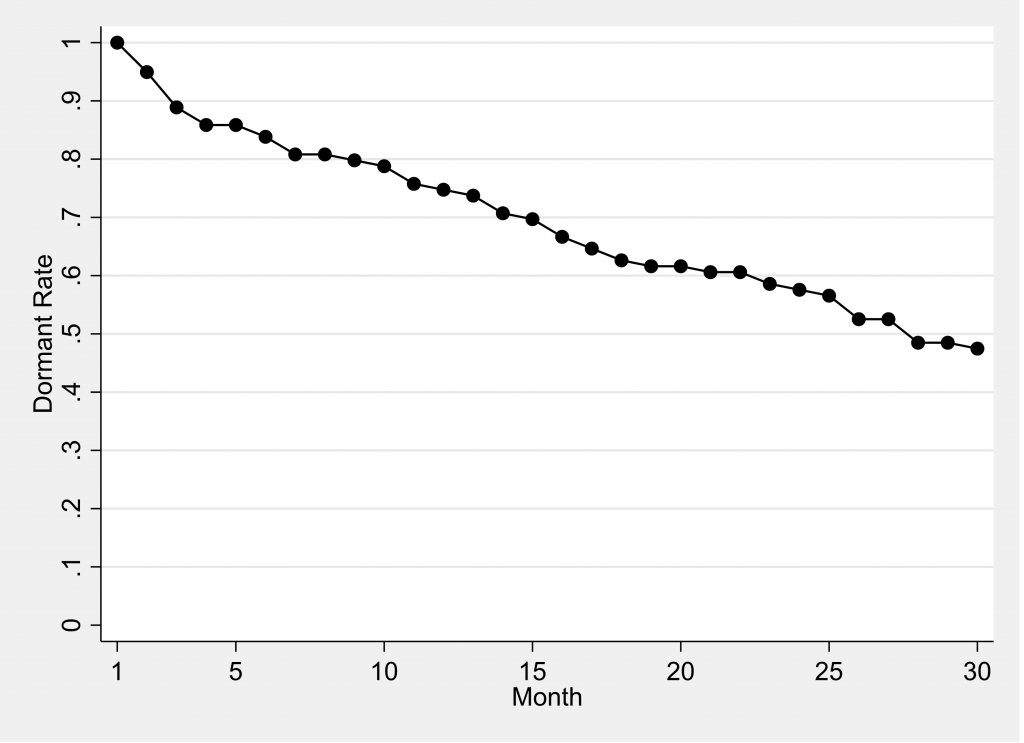
This finding is in contrast to empirical research which found a steady increase in user participation in RWE online spaces as well as studies that conceptualize digital platforms of the extreme right as those that polarize members’ opinions over time. Our study findings do, however, align with other empirical research which suggests that the majority of those who post in RWE online spaces, whether in collective extremist forums for a general audience such as Stormfront or violent RWE forums, tend to desist in and tail of their posting behavior over time. However, our findings may be a symptom of the study sample: each user was either a violent or non-violent RWEs and were actively involved in right-wing extremism. It is reasonable to assume, then, that posting in an open access sub-forum may have become a concern to the users over time, given the offline activities they were engaged in (e.g., violence, illegal activities, organizing rallies, recruiting, etc.). Empirical research on the online behaviors of RWEs suggests those who are actively involved in RWE activities offline are oftentimes concerned that law enforcement officials and anti-racist groups are monitoring their online activities and may modify their posting behaviors to avoid detection. With this in mind, it may be the case that the RWEs in the current study were concerned that, by posting content in an online space that can be publicly viewed, they may be putting themselves in a vulnerable position and could become the subject of an investigation from anti-hate watch-organizations or even law enforcement. Some of the users in the sample may have also been incarcerated during part(s) of study period and were unable to post messages then. Regardless, these findings require further exploration.
From a policy perspective, the results of the current study suggest that analysts who are searching for signs of violent extremists online should be less concerned about investigating high-frequency posters and more concerned about those who post fewer messages online. This is because violent RWEs in the current study posted more messages in the sub-forum in the beginning of their posting careers than the non-violent RWE group but posted less than the non-violent group in the later portions of their posting careers. Violent RWEs also desisted in posting frequency at a much quicker rate than their non-violent counterpart and the only observed characteristic of the violent status was having less total number of posts in the broader forum. In other words, violent RWEs in the current study tended to be those who were much less active online than non-violent RWEs (see Figures 3 and 4).
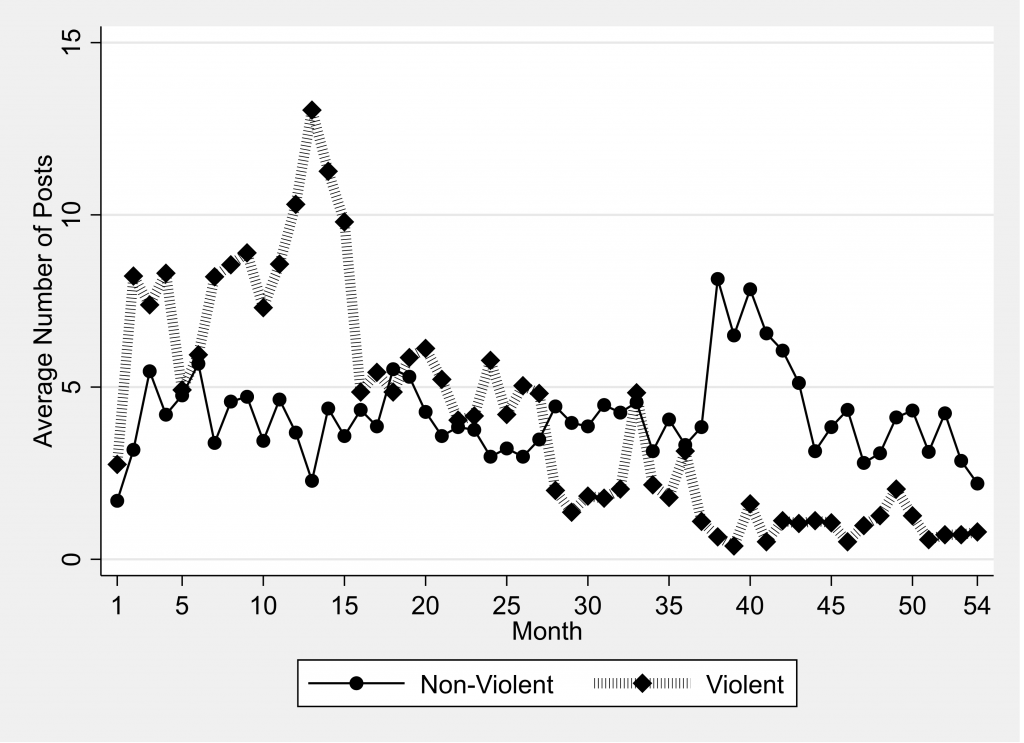
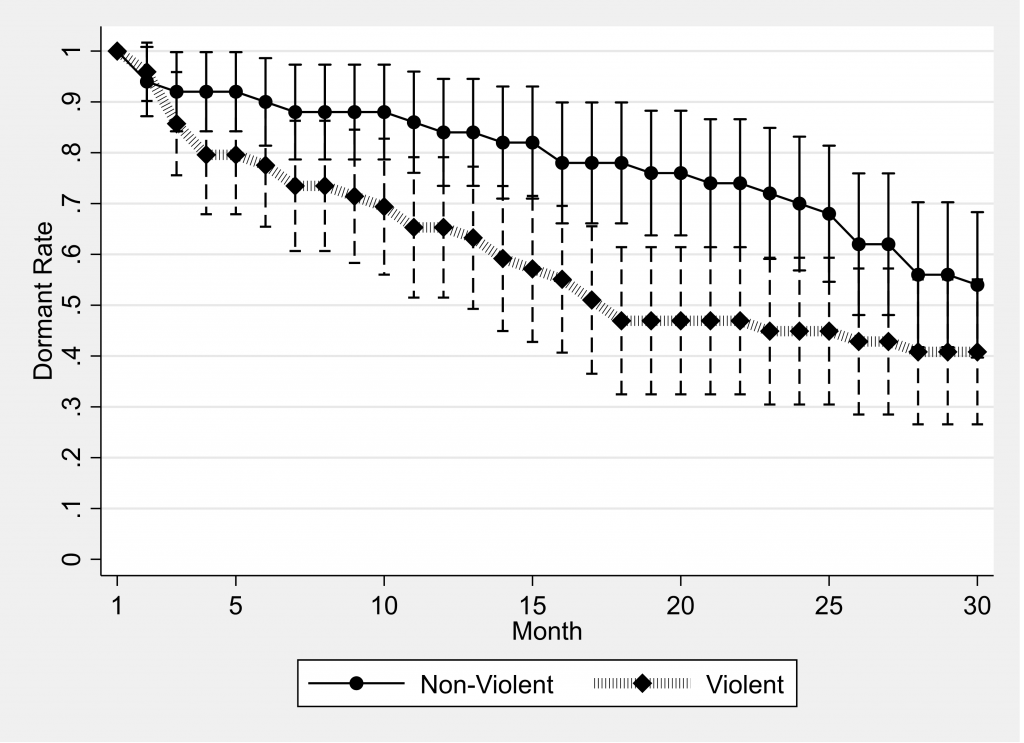
This set of findings is supported by empirical research which found that violent members of RWE movements are largely clandestine, often paranoid because of the violence they engage in, and for this reason are concerned about revealing their identities. Similar to previous research that highlights how some violent RWEs alter their online behaviors to avoid detection from law enforcement, the waning and inactive posting behavior of the violent RWEs in our sample may reflect this security concern. This finding comes as little surprise, given that similar tactics have been adopted by a new generation of RWE who in recent years have exploited various encrypted online platforms and messaging apps to avoid being tracked and detected.
While our analyses provide unique insight into the differences in posting behaviors between violent and non-violent users online, there remain several noteworthy limitations. One limitation pertains to the violence status variable. It is unclear if changes in posting behaviors are driving changes in violent offending or vice versa. Future research should therefore pinpoint exact moments in time that individuals engaged in violence offline and then assess their posting behaviors both before and after the act of violence. Doing so may shed light on whether specific posting behaviors in the online world escalate to violent actions in the offline world.
A second limitation pertains to the data itself. While this type of data is novel in its capacity to provide details about the posting behaviors of violent and non-violent RWEs, it is limited in the information provided by one former extremist. There remain many unanswered questions about the characteristics of those identified as violent or non-violent in our study. Unlike the growing body of research that has drawn distinctions between the offline activities and behaviors of violent and non-violent extremists, our data does not include information on key characteristics identified in this literature such as an individual’s employment status, criminal records, history of mental illness, extremist/radicalised peers, and types of grievances, among many others. Future research is therefore needed to assess whether these characteristics (and others) mirror our sample of violent or non-violent extremists as well as whether certain characteristics drive differential posting behavior.
Lastly, while the novelty of the data in the current study cannot be understated, their validity is based on one key former RWE informant. Future research should further verify the authenticity of each RWE user by identifying the birth and given name of each individual in the sample. These names could then be triangulated with open source intelligence (e.g., media reports, court documents, terrorism databases, and social media accounts on each user) or with the Extremist Crime Database (ECDB), which currently includes over 500 data points on nearly 1,000 violent and 1,500 non-violent RWEs. Triangulating these data may further inform law enforcement and intelligence communities on the online discussions that may result in offline extremist violence as well as shed light on the nexus between the on- and offline worlds of violent and non-violent extremists.
Ryan Scrivens is an Assistant Professor in the School of Criminal Justice at Michigan State University (MSU), an Associate Director at the International CyberCrime Research Centre (ICCRC), and a Research Fellow at VOX-Pol. Follow him on Twitter: @R_Scrivens.
Thomas W. Wojciechowski is an Assistant Professor in the School of Criminal Justice at MSU.
Joshua D. Freilich is a Professor in the Criminal Justice Department and the Criminal Justice PhD program at John Jay College, CUNY.
Steven M. Chermak is a Professor in the School of Criminal Justice at MSU. Follow him on Twitter: @s_chermak.
Richard Frank is an Associate Professor in the School of Criminology at Simon Fraser University and the Director of the ICCRC. Follow the ICCRC on Twitter: @ICCRC_SFU.
